Hackers Invade Cuba’s Wi-Fi Hotspots
Eileen Sosin Martínez (Progreso Semanal)

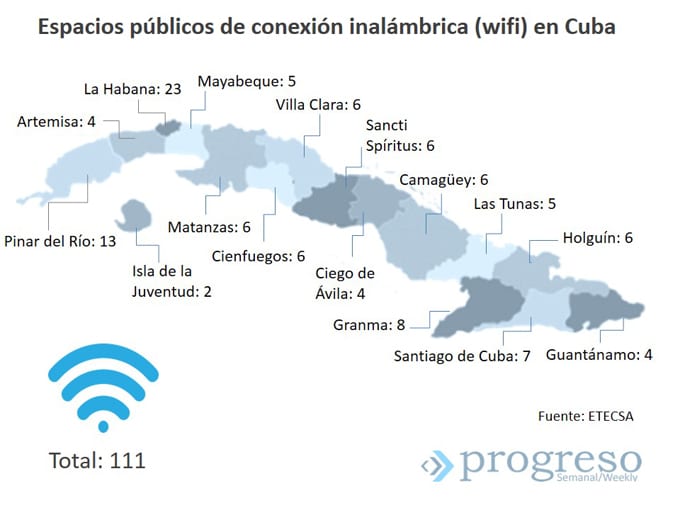
HAVANA TIMES — This time, the rumor – our unofficial news service – is true: Nauta internet accounts are being attacked at Wi-Fi access points. It’s hard for users to detect and its easy for these internet “pirates” to steal connection time. Too easy.
A common way to hack these accounts is to create a false Wi-Fi signal which could be called the same or something similar to ETECSA’s own network. “Phishing involves simulating something in order to access sensitive information,” Andy Velazquez (*), a cybernaut, explains.
For example: when somebody connects to Nauta, they have to first sign in through their registration page, where they have to enter their username and password. What people see is just a design. That’s to say that, with a little web design know-how, you can create a page that looks just like Nauta’s, and trick the ordinary internet user.”
That’s how criminals get their hands on personal details of customers. When they fail to log in, customers think that the server is overcrowded, which is normally the case. The next time this person logs on, two things can happen: the timer shows that they have less minutes than the number they left before; or the system notifies them that another user is connected – with the same details- and therefore are unable to sign in.
In the second case, if the user didn’t take note of how much time they had left, they barely realize, until their credit runs out. “It’s as easy as opening your computer in the middle of a park,” confirms I.T. specialist Camilo Diaz (*).
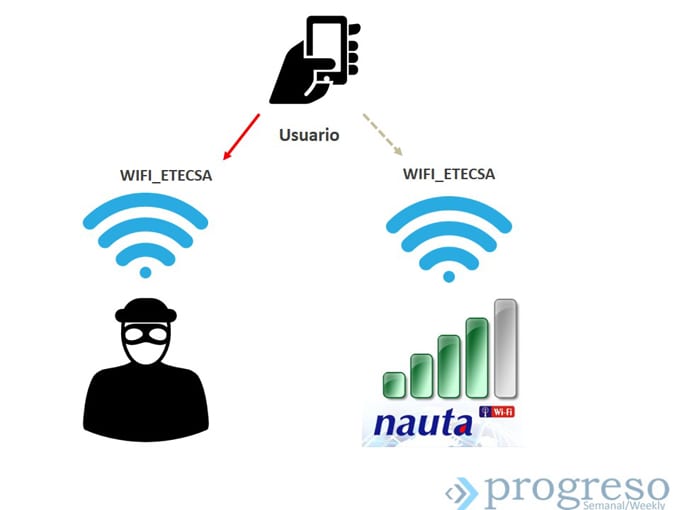
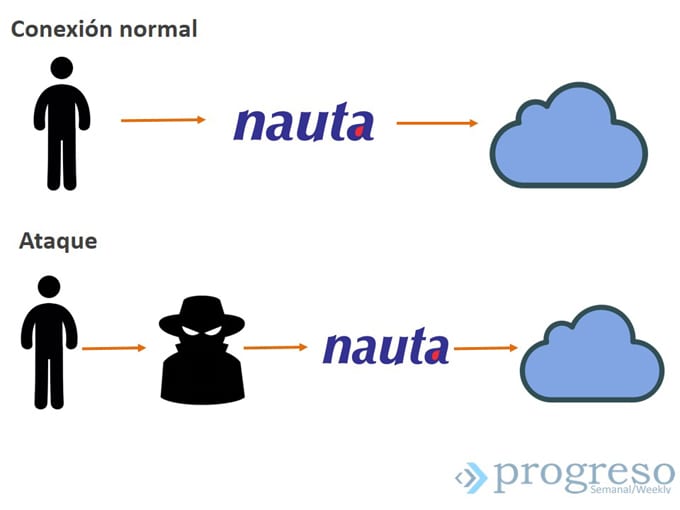
Another case scenario, this time a bit more complex, is the “Man in the middle” technique, which is when the hacker acts as the “middle man” between the internet gateway and the user. In this instance, identity theft also takes place: the “hacker” claims to be ETECSA and all of the customer’s internet traffic goes through him/her.
“In fact, you can even surf the web,” Camilo goes on to tell us, “because you’re giving me your username and password, and I’m going to sign in with this information; and when I do that, I then forward the internet service to you. Therefore, I let you use surf the web for a few minutes so you don’t get suspicious, then I disconnect you, and you’ll just think there are problems with the network, which is normal. Or, I can stay connected, finish what I have to do, and if something bad happens it’s your fault, because I connected using this IP address.”
In that case, users are left extremely vulnerable; only personal measures can be taken to protect yourself from being hacked. Anyway, Andy recommends customers to always look at how much credit they have, when they sign in and log out, and that if they do have problems, that they should report them to ETECSA, and change their username and password immediately.
Mario Carreras (*) doesn’t know when or how his identity was stolen, the only thing he knows is that he had less time remaining than what he had when he next signed onto the WIFI network. Like when you get home and notice there’s something missing. “You can’t just lose five hours,” he notes. However, he hasn’t gone to an ETECSA office to complain about this neither. “Now whenever I connect, I use up all my credit, that way they can’t use my account.”
In this panorama, where some become prisoners and others hunters, Mario has been both. Yes, he too has taken Internet time away from the person next to him, and although he recognizes this “hard to explain” contradiction, it doesn’t seem to eat away at his conscience. “I use somebody else’s internet connection, but maybe that person is stealing it from somebody else too. Because in the end, who will give me back the time that was stolen from me?”
Surfing… gone astray
Brute Force attacks take place regularly across the world: a program begins to systematically try username and password sequences, until it manages to break in. “In reality, sometimes hacking a customer isn’t the service provider’s fault,” Andy points out. “If your name is Fefa and your password is 1234, it wouldn’t take a brute force attack very long to break into your account.” Nevertheless, the Telecommunications Company shouldn’t sit with their arms crossed.
“Have you read Nauta’s contract?” Camilo asks. The truth is I haven’t. But, who reads that anyway? The document has a fine print and you can only get hold of it by standing in line, and the sales exec watches hurry you up because you’ve just signed. Furthermore, if you don’t agree with this contract, it’s not like you have a lot of other options: sign it or don’t sign it; take it or leave it.
 Even so, it explicitly states in the Nauta user agreement contract that, amongst User Responsibilities: “The customer should inform ETECSA of any suspicions they have of fraudulent access to the server using their personal data and passwords. The cost of time used to this end, will be covered by the customer.”
Even so, it explicitly states in the Nauta user agreement contract that, amongst User Responsibilities: “The customer should inform ETECSA of any suspicions they have of fraudulent access to the server using their personal data and passwords. The cost of time used to this end, will be covered by the customer.”
And further on in the document: “ETECSA is exempt from all liability for restricting access to the server (…) as well as the loss of personal data held or used by a third party on your behalf.” In short, there are no police for these thieves. “The text itself is very ambiguous,” Camilo points out, “but basically it exempts ETECSA from all liability and passes it on to you, the consumer.”
Over recent days, the company has developed a Consumer Protection campaign which includes its website and its social network accounts. Complaints, claims and queries can be written to the email address [email protected] (the contract also states this). However, writing to them as a consumer trying to find out about this phenomenon, I received no response from ETECSA. On Twitter neither.
If you ask about the same thing by calling 118, the Commercial Information and Consumer Protection helpline, Daniela responds, “With WIFI? They’re stealing passwords?… We don’t know anything about that.” We try again and Deysi assures us, “We have no knowledge that this is happening.”
Once again and Anabel repeats, “Here at ETECSA, we have no information regarding this subject.” I insist a little, and the woman’s tone becomes a little more impatient: “Look, young lady, you know that there are people who dedicate themselves to robbing everything,” and adds that if I connect “normally” from my mobile phone, nothing will happen; the account “is caught” when somebody tries to connect via other people, and that maybe that’s where they get conned. “However, ETECSA has no problems with its WIFI network,” she rounds off, convinced.
Nonetheless, the company knows what’s really going on. On the Mesa Redonda TV program aired on March 30, the I.T. technician Eliecer Samada, warned that there are “unscrupulous people who are stealing other users’ personal information, and then they use up what’s left on the account, or sell it on. “This customer, when he manages to realize what’s happened, doesn’t know who to report this too, and the system doesn’t pick up on these kinds of breaches because there hasn’t been any abnormal behavior when logging in.”
The customer – stuck in the “the customer’s always right” philosophy – knows who to complain to. At the shopping center in the Focsa Building (in Vedado), a caretaker confirms that a lot of people come every day with the same problem, and the only way to resolve it is to change your username and password. That’s it. And if they hack your account again, you have to change your personal information again. “Don’t sit near laptops,” the man advises, in a secretive whisper.
Camilo thinks the root cause of this problem lies in the Security Certificate that ETECSA uses, which hasn’t been certified by any international organization. This explains the warning that pops up when users register for the first time. “The browser can’t detect that it’s connected to ETECSA’s website 100%, because it doesn’t have a valid certificate.” WIFI networks are established on collaboration servers, which weren’t made to resist attacks.
Passed by the Ministry of Information and Communication, Resolution 127 / 2007 lays out the Security Regulations that Information and Communication Technologies need to abide to. This law is directed mainly at institutions, as individual users don’t exist, and doesn’t mention anything about WIFI networks.
Of course, when this law was approved, the Internet wasn’t so widespread and public WIFI points didn’t exist. In terms of information and communication technology, a law that came into effect 10 years ago is the same as being governed with last century’s laws.
“We don’t have “to finish off the hackers”: hackers exist because basic needs aren’t being met,” Camilo declares. In his opinion, the solution involves signing a valid Security Certificate, without fail. And he dares to venture: “Maybe it sounds a bit surreal, but Cuba didn’t think twice about making a whole lot of things free. Why can’t WIFI be one of those things?”
Mario (the hunter-hunted) shares a similar thought: “For me, the only way out of this problem is to reduce the connection price. At the end of the day, Internet isn’t a luxury; it helps us learn, to communicate and to fix problems… It improves our quality of life.”
——
(*) Names have been changed at the interviewees’ request.






This is nothing new, it started immediately after the WiFi hotspots started to open up.
WIFI socialism seems a natural. It should be free to all Cuban’s.